Bitcoin's Transparency Problem
When Satoshi Nakamoto described Bitcoin in 2008, the whitepaper was explicit: transactions are recorded on a public ledger visible to anyone. At the time, this was considered acceptable — users were identified only by addresses, not real names. But this model has not held up to scrutiny.
Every Bitcoin address you've ever used, every amount you received or sent, and every wallet you transacted with is permanently visible on the blockchain. Chain analysis firms like Chainalysis have built entire businesses around de-anonymizing Bitcoin users by tracing transaction graphs, connecting addresses to exchange accounts (which require ID), and following the money through the network.
If you've ever received BTC from an exchange, that exchange knows which address you withdrew to. If you spent from that address, the recipient can see your entire incoming transaction history. This applies even if you never gave anyone your real name.
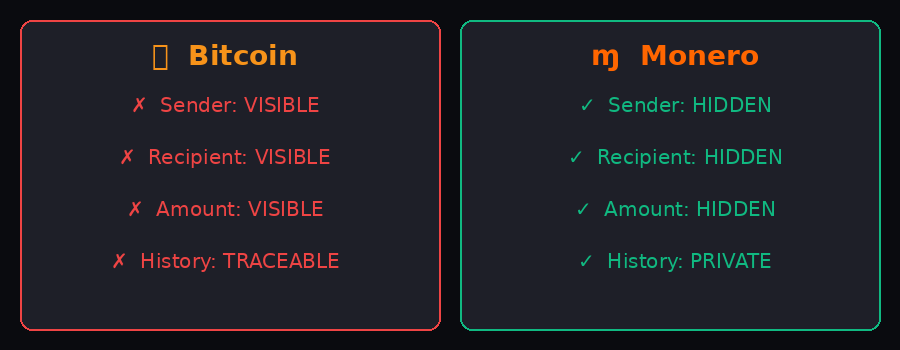
What's visible on Bitcoin's blockchain
Sender address — fully visible to anyone
Recipient address — fully visible to anyone
Transaction amount — fully visible to anyone
Full transaction history of any address is traceable forever
What's visible on Monero's blockchain
Sender hidden — ring signatures obscure origin
Recipient hidden — stealth addresses, one-time use
Amount hidden — RingCT encrypts transaction values
No tracing — past or present transaction history unreadable
How Monero Hides Transactions
Monero doesn't rely on a single trick. It uses three distinct cryptographic mechanisms that each address a different layer of the privacy problem. All three are applied automatically to every transaction — users don't have to opt in.
1. Ring Signatures — Hiding the Sender
How it works
When you send Monero, your wallet doesn't just sign the transaction with your private key. Instead, it creates a "ring" by pulling in a set of other past transaction outputs from the blockchain as decoys. Your actual output is mixed with these decoys, and a ring signature proves that one of the ring members authorized the transaction — without revealing which one.
As of 2022 (Monero's Fluorine Fermi hard fork), every transaction uses a ring size of 16 members. An outside observer sees 16 possible senders and cannot determine which one actually spent the coins. The more transactions on the network, the more plausible decoys exist, and the stronger this protection becomes over time.
2. Stealth Addresses — Hiding the Recipient
How it works
In Bitcoin, if you publish your address, anyone can see every payment you've received. Monero solves this with stealth addresses. When you share your Monero address, senders use it to generate a one-time, mathematically unique address for that specific payment. The XMR lands in this new address, which only you can spend (using your private view key to scan the blockchain).
The result: your published Monero address is never directly linked to any transaction on the blockchain. Someone who knows your address still cannot find your balance or transaction history by searching the chain.
3. RingCT and Bulletproofs — Hiding the Amount
How it works
Ring Confidential Transactions (RingCT), introduced in 2017, encrypt the amounts in every Monero transaction. The amounts are hidden using Pedersen commitments — a cryptographic technique that lets the network verify a transaction is valid (outputs don't exceed inputs) without knowing the actual numbers.
Bulletproofs, activated in 2018, reduced the size of range proofs required by RingCT by about 80%, significantly cutting transaction fees while preserving the same mathematical guarantees.
Full Feature Comparison: XMR vs BTC
| Feature | Bitcoin (BTC) | Monero (XMR) |
|---|---|---|
| Transaction sender hidden | No (address visible) | Yes (ring signatures) |
| Transaction recipient hidden | No (address visible) | Yes (stealth addresses) |
| Transaction amount hidden | No | Yes (RingCT) |
| Privacy is default | No | Yes (always on) |
| Blockchain analytics possible | Yes (Chainalysis, etc.) | No practical analysis |
| Fungibility | Partial (tainted coins) | Full (all XMR identical) |
| View key for auditing | N/A | Yes (optional disclosure) |
| Mining algorithm | SHA-256 (ASIC dominated) | RandomX (CPU-friendly) |
Who Uses Monero and Why
The most common reason people swap Bitcoin for Monero is simple: they don't want their financial activity visible to anyone who looks. This covers a wide range of entirely ordinary situations.
Businesses and freelancers
A freelancer paid in Bitcoin reveals their income to anyone who knows their address. A business that pays suppliers in BTC exposes its vendor relationships and payment amounts to competitors. Monero removes this exposure.
Individuals protecting personal finances
Using Bitcoin to pay for something reveals to the merchant — and anyone analyzing the blockchain — how much BTC you hold in the sending address. This creates security risks (targeted theft, social engineering) that Monero eliminates by design.
People in high-surveillance environments
Journalists, activists, and people in countries with capital controls often use Monero because financial surveillance is a real threat in their context. Privacy isn't a luxury when your government or an adversary can see every transaction.
On fungibility: All Monero coins are identical in practice. No XMR has a "history" that makes it less acceptable. In contrast, Bitcoin that passed through certain services can be flagged by exchanges and refused. Monero's privacy makes it genuinely fungible — the way cash is.
What Monero Doesn't Protect Against
Monero protects the blockchain layer. It does not automatically protect against other privacy leaks.
Network-level surveillance
When you broadcast a Monero transaction, your IP address is briefly linked to it by nodes on the network. Monero uses Dandelion++ to make IP-to-transaction linking harder, but for the strongest protection, broadcasting over Tor or a VPN is recommended.
Exchange records
If you buy XMR from a centralized exchange that required KYC, that exchange has a record linking your identity to the transaction. The exchange doesn't know where you send the XMR after withdrawal, but the initial acquisition is recorded.
Operational security
If you tell someone your Monero address, they now know you received whatever was sent to it (though not from whom, and not any other transactions). Privacy tools only work when combined with careful handling of who knows what.
Exchange Bitcoin for Monero — no KYC, no account
Swap BTC to XMR in under 5 minutes. Rate locked at time of exchange.
Swap BTC → XMR NowMonero vs Bitcoin Privacy: A Technical Comparison
Both Bitcoin and Monero are decentralized cryptocurrencies, but their privacy models are completely different. Here's a side-by-side breakdown of every privacy-relevant property:
| Property | Bitcoin (BTC) | Monero (XMR) |
|---|---|---|
| Sender identity | Public on blockchain | Hidden (ring signatures) |
| Recipient identity | Public on blockchain | Hidden (stealth addresses) |
| Transaction amount | Fully visible | Hidden (RingCT) |
| Transaction graph | Fully traceable | Not linkable |
| Address reuse privacy | Each reuse links history | Stealth addresses prevent this by default |
| Privacy opt-in required | Yes (CoinJoin, Lightning) | No — private by default |
| Chain analysis feasibility | High (Chainalysis, Elliptic) | Not practically feasible |
| IP leak (tx broadcast) | Without Tor: exposed | Dandelion++ + Tor recommended |
| Fungibility | No (tainted coins) | Yes — every XMR is equal |
| Supply auditable | Fully transparent | Yes but via cryptographic proofs |
Dandelion++: How Monero Protects Your IP at Broadcast Time
When you send a Monero transaction, it needs to be broadcast to the peer-to-peer network. In Bitcoin, this broadcast is immediate and direct — your node sends the transaction to its peers, and those peers can correlate the first-seen IP address with the transaction.
Monero uses Dandelion++, a protocol that changes how transactions propagate. Instead of immediately broadcasting to all peers ("fluff phase"), the transaction first travels along a random path of nodes in "stem phase" — each node privately passing it to the next without broadcasting. After a random number of hops, the transaction enters "fluff phase" and spreads normally.
The result: even a network observer who monitors many Monero nodes cannot easily determine which IP originated a given transaction, because the originating node never broadcasts it — only a downstream node does, after multiple hops.
For even stronger protection, Monero wallets like Feather Wallet and Monerujo support routing transactions through the Tor network before they reach any Monero node at all.
The Taint Problem: Why Bitcoin Fungibility Fails
Fungibility means that every unit of a currency is interchangeable with every other unit. A $10 bill from a convenience store is worth the same as a $10 bill from a drug deal — banks don't ask where your cash came from (usually). Cash is fungible.
Bitcoin is not fungible. Because every transaction is on a public ledger, chain analysis firms can trace the history of any Bitcoin through every owner. "Tainted" coins — Bitcoin that previously passed through sanctioned entities, darknet markets, or hacks — are sometimes refused by exchanges or flagged by compliance systems. This means two people holding 1 BTC each may not actually have the same value: one's BTC might be freely tradeable, the other's might be flagged on 5 exchanges.
This creates a real problem for Bitcoin's monetary properties. If coins with "bad" histories are worth less, Bitcoin is stratified — it's not one currency but many depending on provenance. This undermines its value as a neutral money.
Monero solves this entirely. Because no transaction history is visible, there are no tainted XMR coins. Every Monero is indistinguishable from every other Monero. The miner who just received block rewards holds XMR that is cryptographically identical to XMR from any other source. This is true fungibility.
Monero Auditing: Can You Prove Your Transactions If Needed?
Monero's privacy is default-on, but it includes mechanisms for voluntary disclosure when you choose to share information:
Transaction key (tx_key): For any transaction you send, you can provide the transaction key to a third party. With this key and the recipient's address, they can cryptographically prove the transaction amount and destination. This is used for audits, disputes, or proof of payment.
View key: You can share your wallet's view key with an auditor, accountant, or compliance officer. With the view key, they can see all incoming transactions to your wallet without being able to spend anything. This enables transparent auditing for businesses or individuals who need it.
Spend key: Never share this. It allows spending. Keep it equivalent to your wallet password or seed phrase.
This design is important: Monero's privacy is not "we can't see it either." The user controls disclosure. You can prove anything you need to prove to anyone you choose, while everything stays private from everyone else.
Real-World Privacy Attacks on Bitcoin: What Happens Without Monero
Exchange clustering attacks
Chain analysis firms like Chainalysis maintain large databases of known Bitcoin addresses — exchange deposit addresses, known wallets, flagged entities. When your Bitcoin touches any known address, it creates a link. Even if you receive Bitcoin from a privacy-conscious source, spending it to a KYC exchange de-anonymizes the entire UTXO set linked to that transaction.
Change address tracking
When you send Bitcoin, the "change" (remaining amount) goes back to an address in your wallet. Chain analysis can follow this change address through subsequent transactions to track your entire Bitcoin history even across multiple wallets.
Dust attacks
An attacker sends tiny amounts of Bitcoin ("dust") to your address, then watches to see which other UTXOs it gets combined with when you spend — revealing your address clusters and wallet ownership.
None of these work on Monero
Ring signatures prevent input linking. Stealth addresses prevent output clustering. RingCT prevents amount-based analysis. Dandelion++ prevents IP correlation. The entire attack surface that chain analysis firms exploit on Bitcoin simply does not exist in Monero's protocol.
Frequently Asked Questions About Monero Privacy
There have been no confirmed cases of Monero transactions being traced by blockchain analysis. In 2020, the IRS offered $625,000 contracts to companies to crack Monero — CipherTrace claimed partial results for tracing on-chain, but independent verification was never provided and the claim was disputed by cryptographers who reviewed their methodology. The general consensus among cryptographers is that Monero's on-chain privacy is sound.
Yes, for several reasons. Bitcoin mixers require trusting the mixer not to log your transaction. They are also distinguishable on the blockchain — using a mixer is itself a flag. Monero's privacy is built into the protocol, requires no additional trust, and is indistinguishable from any normal Monero transaction. There's no "privacy transaction" that stands out — every Monero transaction looks identical.
Several major centralized exchanges have delisted XMR under regulatory pressure, particularly in Europe and the US. This reduces accessibility through KYC channels but does not affect the protocol itself. No-KYC swap services like btcswapxmr.com fill this gap. Monero's decentralized network continues to operate normally regardless of exchange listings.
Yes. Monero has a growing but still limited merchant acceptance compared to Bitcoin. You can pay for VPN services (Mullvad, ProtonVPN), privacy-focused hosting, and some other products. The Monero community maintains a directory of accepting merchants at monerica.com. For wider everyday use, the XMR→BTC swap route gives you access to Bitcoin's wider acceptance while maintaining privacy for the XMR portion.